What You Need to Know
Gmail and Outlook dominate email, but they come with privacy trade-offs. Your messages pass through corporate servers where algorithms scan content for ads and data mining. Setting up your own email server puts you back in control, ensuring only you can access your communications.
This guide walks you through creating a private email server with robust spam filtering and security features. You’ll need basic Linux knowledge and about 2-3 hours for initial setup. The process involves configuring multiple components that work together: a mail transfer agent, spam filters, and security protocols.
Running your own server requires ongoing maintenance, but the privacy benefits are substantial. You control data retention, encryption standards, and user access. Plus, you’ll learn valuable skills about email protocols and server administration.

1. Choose Your Server Environment
Start with a Virtual Private Server (VPS) from providers like DigitalOcean, Linode, or Vultr. Shared hosting won’t work for email servers due to port restrictions and resource limitations. Your VPS needs at least 1GB RAM and 20GB storage, though 2GB RAM provides better performance.
Install Ubuntu Server or Debian as your operating system. These distributions have extensive documentation and stable package repositories for email software. Avoid desktop versions – server editions use fewer resources and have better security defaults.
Configure your domain’s DNS records before proceeding. Add MX records pointing to your server’s IP address, and set up A records for your mail subdomain. This step is crucial – without proper DNS configuration, other email servers will reject your messages.
2. Install and Configure Postfix
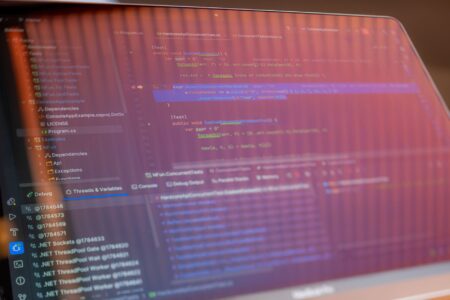
Postfix serves as your Mail Transfer Agent (MTA), handling message routing and delivery. It’s more secure and easier to configure than alternatives like Sendmail. Install it using your distribution’s package manager and select “Internet Site” during setup.
Edit the main configuration file at /etc/postfix/main.cf to customize your setup. Set your hostname, domain name, and network interfaces. Enable SASL authentication to prevent unauthorized users from sending mail through your server. Configure TLS encryption for secure communication with other email servers.
Create virtual mailboxes to separate email storage from system user accounts. This approach improves security and makes user management easier. Define virtual domains and aliases in separate files that Postfix references during message processing.
3. Set Up Dovecot for Email Access
Dovecot handles IMAP and POP3 protocols, allowing email clients to retrieve messages from your server. It also manages local delivery and provides authentication services for Postfix. Install Dovecot and configure it to work with your virtual mailbox setup.
Enable SSL/TLS certificates for secure client connections. Use Let’s Encrypt for free certificates that automatically renew. Configure authentication mechanisms compatible with popular email clients like Thunderbird, Apple Mail, and mobile apps.
Set up mailbox quotas to prevent users from consuming excessive disk space. Configure automatic mailbox creation for new users and establish folder structures for organizing messages. Test IMAP connectivity using telnet or openssl commands before configuring client applications.

4. Implement Spam Protection
SpamAssassin provides content-based spam filtering using heuristic analysis and community-maintained rules. Install it alongside Postfix and configure integration through the spamass-milter interface. This setup screens incoming messages before delivery to user mailboxes.
Complement SpamAssassin with DNS-based blacklists (DNSBLs) that block messages from known spam sources. Configure multiple blacklist providers for comprehensive coverage, but avoid overly aggressive lists that might block legitimate mail. Set up whitelists for trusted senders and domains.
Install ClamAV for virus scanning to protect against malware attachments. Configure it to scan both incoming and outgoing messages. Set up automatic signature updates to maintain protection against new threats. Consider implementing greylisting as an additional spam reduction technique.
5. Configure SPF, DKIM, and DMARC
These authentication protocols help other email servers verify that your messages are legitimate. SPF records specify which IP addresses can send mail for your domain. Create SPF records in your DNS that authorize your server’s IP address and reject unauthorized sources.
DKIM adds cryptographic signatures to outgoing messages. Install OpenDKIM and generate signing keys for your domains. Publish public keys in DNS TXT records and configure Postfix to sign outgoing mail. This prevents message tampering and improves deliverability.
DMARC policies tell receiving servers how to handle messages that fail SPF or DKIM checks. Start with a monitoring policy to collect reports about your domain’s email authentication. Gradually move to stricter policies as you verify your setup works correctly.
6. Enhance Security and Monitoring
Configure firewall rules to restrict access to essential ports only. Allow SMTP (25), IMAP (993), and POP3 (995) for encrypted connections while blocking unencrypted alternatives. Install fail2ban to automatically block IP addresses that attempt brute force attacks against your mail services.
Set up log monitoring to track delivery issues, authentication failures, and spam attempts. Tools like Logwatch provide daily summaries of system activity. Configure alerts for critical events like service failures or unusual traffic patterns.
Implement regular backups of your mail directories and configuration files. Automated backup systems can sync critical data to cloud storage for disaster recovery. Test restore procedures periodically to ensure your backups work correctly.

Key Takeaways
Running your own email server requires significant technical commitment but delivers unmatched privacy control. The initial setup involves multiple interconnected components – Postfix for mail routing, Dovecot for client access, and various security tools for spam protection.
Success depends on proper DNS configuration and ongoing maintenance. Monitor delivery rates and reputation scores to ensure your messages reach their destinations. Keep software updated and maintain current SSL certificates to prevent security vulnerabilities.
Consider the operational overhead before committing to this approach. Email servers need 24/7 uptime and quick response to issues that could block legitimate communications. However, for users prioritizing privacy and control over convenience, a custom email server provides the ultimate solution for secure communications.
Frequently Asked Questions
How much does it cost to run your own email server?
Basic VPS hosting starts around $5-10 monthly, plus domain registration fees.
Is running your own email server difficult?
It requires Linux knowledge and ongoing maintenance, but provides complete privacy control.